Safety vulnerability ID: 38487
The information on this page was manually curated by our Cybersecurity Intelligence Team.
Misp-maltego 1.4.5 resolves an information disclosure vulnerability when using MISP-maltego as remote transform server. The transform server would cache the MISP credentials of the first user connected, and provide access to that MISP instance for any later user. See: CVE-2020-12889.
Latest version: 1.4.7
Maltego transform for interacting with a MISP Threat Sharing community and with MITRE ATT&CK.
Searching with `%` wildcards
While the Galaxies already supported sub-string search this feature is extended to all the supported Maltego entities. From now you can use the `Search in MISP` transform on any Maltego entity.
As with the MISP attribute search through the MISP Web UI you can use `%` wildcards at the front and end to specify the substring. You might be tempted to always use `%keyword%`, but bare in mind how databases indexes work; a search for `keyword%` will always be much faster than `%keyword`.
Massively large MISP event? Think before you transform.
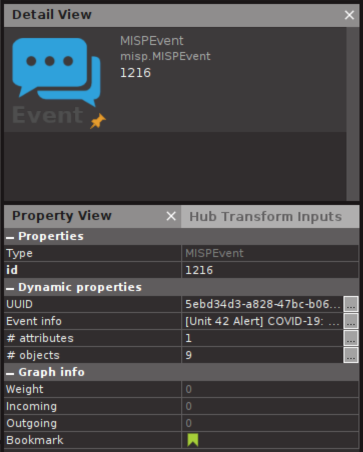
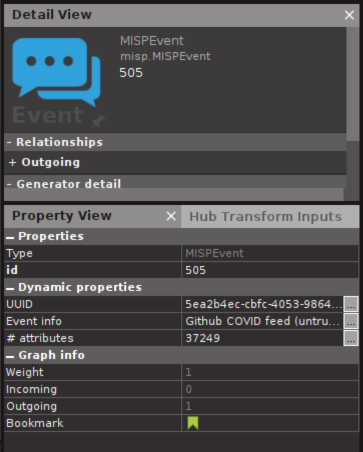
In some communities such as the [COVID-19 MISP](https://www.misp-project.org/covid-19-misp/) some events contain tens of thousands attributes. Loading all the attributes from these events might not be a good idea if you do not have Maltego XL.
From now on you can see the amount of attributes and objects in the Event properties, so you can think before you click:
Various improvements and security fix
This release resolves an information disclosure vulnerability when using MISP-maltego as remote transform server. The transform server would cache the MISP credentials of the first user connected, and provide access to that MISP instance for any later user. (CVE-2020-12889).
This release also brings various improvements:
- Tag to Event massive performance boost
- Minor fixes in Machines who were not working as expected
- Minor code cleanups
Scan your Python project for dependency vulnerabilities in two minutes
Scan your application